A New Hope for IoT Security?
With the constantly rising number of connected devices also rises the number of IoT-based cyber-attacks, such as when the Mirai botnet launched one of the largest and most powerful distributed denial of service (DDoS) attacks on DNS provider Dyn and its customers, temporarily rendering services like Twitter, Reddit, and Spotify inaccessible.The situation has become so bleak that the US Congress even proposed an Internet of Things Cybersecurity Improvement Act to force the manufacturers of connected devices, such as webcams, printers, light bulbs, or home routers, to comply with what the regulators call minimal cybersecurity operational standards for IoT devices.
Currently, statistics show that there are approximately 20 billion connected devices worldwide, and some, such as ARM and SoftBank Chairman Masayoshi Son, expect a trillion connected devices by 2035. But unless IoT security fundamentally improves, we could be headed toward what can only be described as IoT apocalypse.
“These attacks have highlighted the very real need for better security measures to be implemented, throughout the value chain of connected devices, covering high-level infrastructure, such as energy supply and connected vehicles to low-cost devices, such as webcams and smart lighting. Breaches in security present a host of issues for those operating in the IoT. Leaks in confidential information, theft of personal data, a loss of control of connected systems and the shutting down of critical infrastructure, all represent major areas at risk,” states ARM on its community blog.
Considering how many IoT devices are built on the ARM architecture, which is known for its remarkable efficiency, and considering that the British multinational semiconductor manufacturer expects to have shipped 200 billion ARM-based chips by 2021, it’s easy to see why ARM might be interested in taking IoT security into their own hands to ease some of the concerns legislators and the general public already have.
Recently, almost exactly a year after Masayoshi Son announced his vision for a trillion connected devices by 2035 at Arm TechCon, ARM announced its open source Platform Security Architecture (PSA), which is described as an holistic set of threat models, security analyses, hardware and firmware architecture specifications intended to serve as a secure foundation for connected devices.
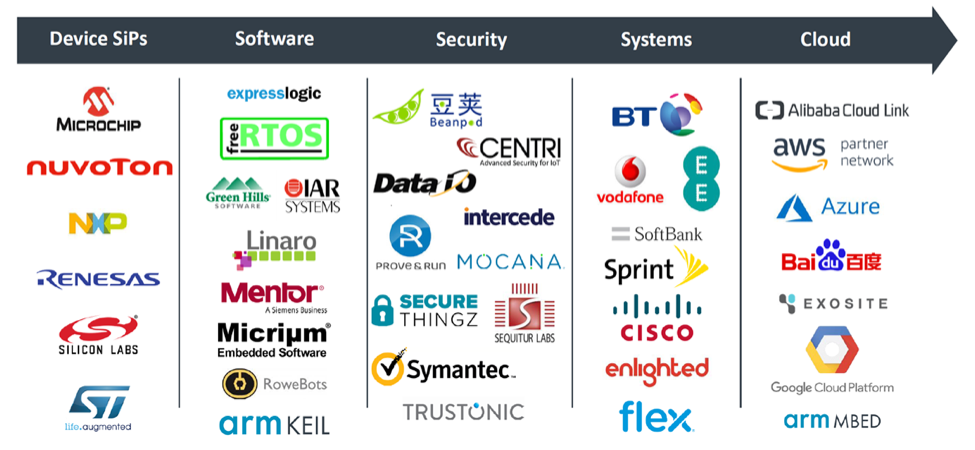
Some of the biggest names in the industry are already supporting PSA, including Google, Microsoft, Cisco, Vodafone, Symantec, SoftBank, and Alibaba, just to name a few.
According to Paul Williamson, vice president and general manager of IoT Device IP at ARM, “The growing number of devices being connected to the internet need to be secure without sacrificing the very diversity which make them innovative and unique. ARM chief system architect Andy Rose and his team made sure this was top of mind when developing PSA through analysis of devices and best practices for securing them.”
As such, PSA delivers hardware and firmware architecture specifications, built on key security principles, defining a best practice approach for designing endpoint devices and a reference open source implementation of the firmware specification, called Trusted Firmware-M, which is designed to work with the company’s ARMv8-M processor architecture. Trusted Firmware-M is scheduled for release in early 2018.
According to Naked Security, Trusted Firmware-M makes possible:
- A proper root of trust.
- A protected crypto keystore.
- Software isolation between trusted and untrusted processes.
- A way of securely updating firmware.
- Easy debugging down to chip level.
- A reliable cryptographic random number generator.
- On-chip acceleration to make crypto run smoothly.
Considering how many major industry players already stand behind ARM’s effort, it seems that the release of Trusted Firmware-M in early 2018 could be the tipping point that so many of those who have been preaching about the growing need for improved IoT security have been waiting for.
The last few years proved that IoT vendors cannot be relied on when it comes to securing their products as the entire world witnessed the consequences of poor security practices such as including weak default passwords in hardware or never releasing security updates to patch critical vulnerabilities.
ARM’s bottom-up approach to IoT security seems like the only reasonable way to go at this point, providing a strong incentive for IoT vendors to build their products using ARM’s cost-effective, scalable, easy-to-implement security framework.
“The value of the ARM ecosystem is to provide diversity and choice to end-customers, and this benefit extends to the IoT and its broad range of technologies and providers. ARM recognizes this potential, alongside the risks that threaten the devices, systems, and infrastructures operating within the IoT. PSA provides the common framework for the ecosystem, from chip designers and device developers, to cloud and network infrastructure providers and software vendors,” states ARM.



